Table of contents
Introduction
In this article, I will be talking about what are TCP/IP, three-way handshake, and TLS handshake.
TCP/IP
Transmission Control Protocol (TCP) is a protocol that is used to send data to someone just like a message. TCP is similar to a puzzle, where the entire puzzle is broken down into smaller pieces, and we combine them to make it one. In TCP, the data is chopped into pieces and travels through different routes, some of which can take a longer time than others.
The Internet Protocol (IP) ensures that those puzzles (smaller pieces of data) arrive at the correct destination.
TCP is used in conjunction with IP in order to maintain a connection between the sender and the target (destination) and to ensure packet order.
TCP Characteristics:
Uses a 3-way handshake to establish a connection and a 4-way handshake to terminate the connection.
Reliable (data is not duplicated, lost, etc)
Slower than UDP
TCP Three-way Handshake
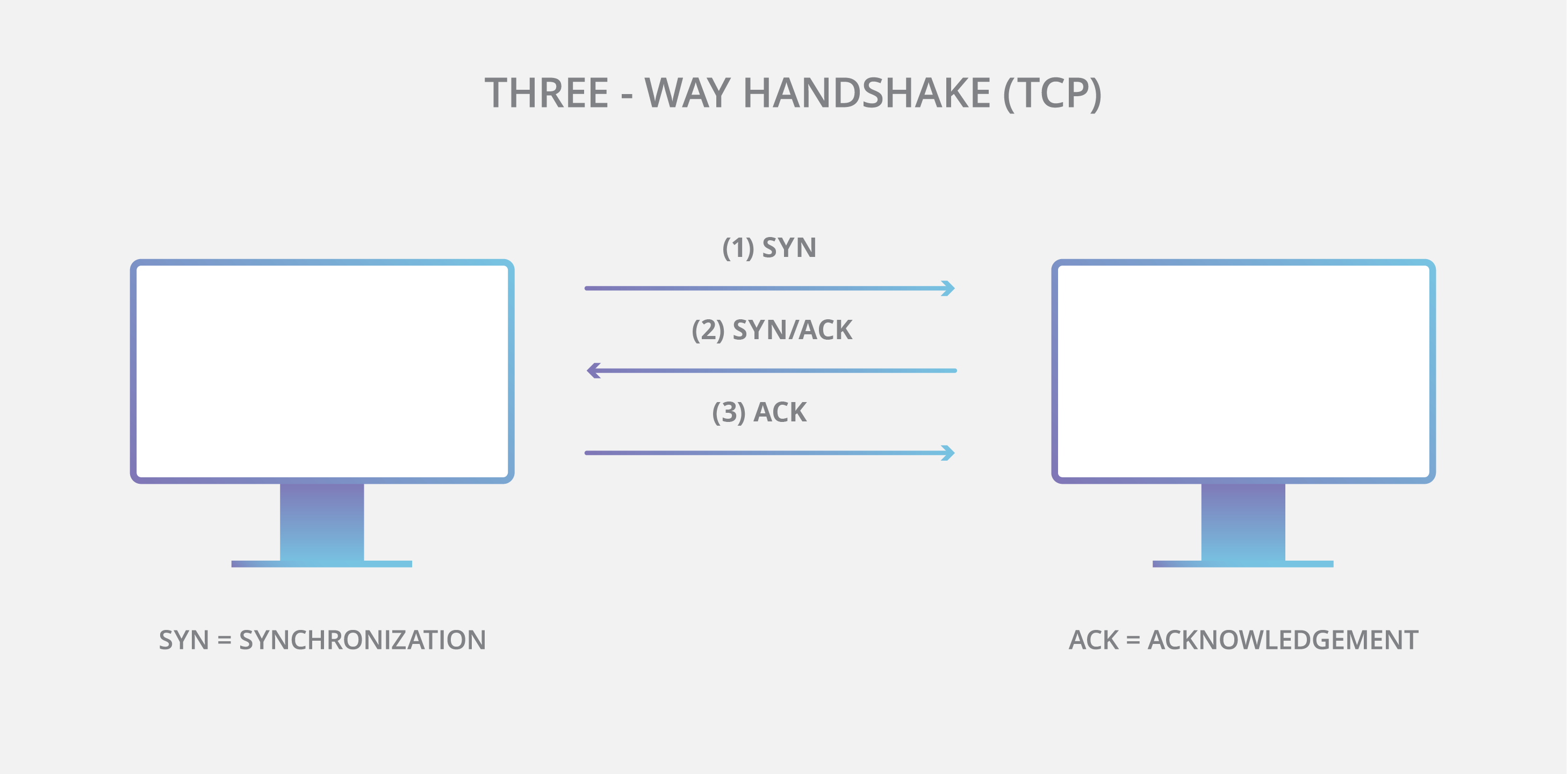
A three-way handshake is used to verify the data and establish a connection. It is to ensure that both sides (client & server) are ready to communicate and send/receive data. Whenever the data is transmitted via TCP, a 3-way handshake occurs.
Three-way handshake process:
The source sends an SYN “initial request” packet to the target server to start the dialogue.
PORT status:
client:
CLOSED-->SYN_SENTserver:
LISTEN
The target server sends a SYN-ACK packet to agree to the process.
PORT status:
client:
CLOSEDserver:
SYN_RCV
The source sends an ACK packet to the target to confirm the process, after which the message contents can be sent.
PORT status:
client:
ESTABLISHEDserver:
SYN_RCV-->ACK-->ESTABLISHED
TLS Handshake
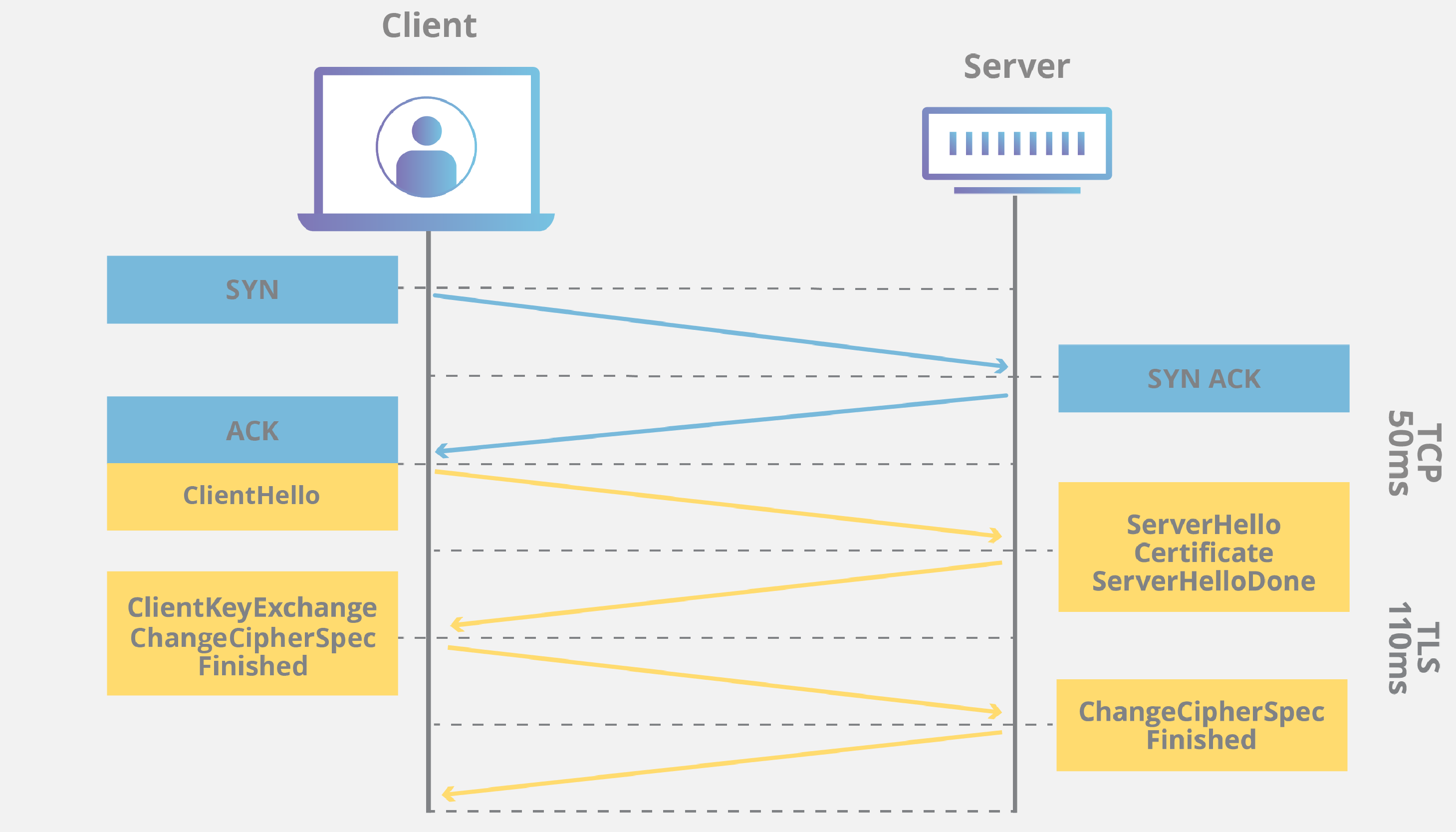
A TLS handshake is the process that starts a communication session that uses TLS. TLS is an encryption and authentication protocol. Just like the three-way handshake was to establish a connection and verify the data, TLS "handshake" is also used to acknowledge each other, verify each other, establish the cryptographic algorithms and agree on session keys.
Reference
https://www.cloudflare.com/learning/ddos/glossary/tcp-ip/
https://www.cloudflare.com/learning/ssl/what-happens-in-a-tls-handshake/